BitLocker Password Recovery
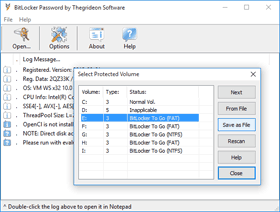
BitLocker Password by Thegrideon Software is an advanced password recovery tool for BitLocker encrypted volumes and BitLocker to Go protected devices (such as internal and external hard drives, USB flash drives, etc.).
BitLocker Password can be used to search for user-set passwords to unlock only. ![]() You may also check Password Search FAQ.
You may also check Password Search FAQ.
BitLocker Password Recovery Features:
- BitLocker records can be loaded from local disks as well as from partition / disk images.

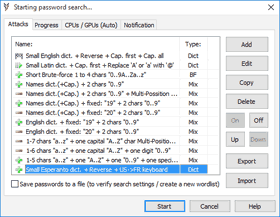
- Several password search attacks can be configured and queued:
- advanced mixed attacks for precise search range setup:
- multi-position moves to cover modern password policies;
- simple modifications: add part(s) copy, replace chars, etc.
- typing errors, case switching, char substitutions;
- brute-force attacks based on a charset and length selected:
- limit number of equal, capital or special chars or digits;
- dictionary attacks with modifications (several wordlists are included):
- advanced keyboard layouts-aware recovery technique;
- password in reverse, capitalized, uppercased, lowercased;
- number ranges (e.g. 1-31, 01-12, 2013-2020, etc.);
- "Output attacks to a file" option to verify search settings, generate new wordlist, etc.
- Highly optimized code (SSE, AVX, AVX2, AVX-512) guarantees best performance.

- Utilizes NVIDIA and AMD Graphics processing units with high-performance methods.
- Utilizes modern integrated Intel GPUs as well.

- Supports up to 64 simultaneous processing threads (multi-CPU, multi-GPU).
- Audio, script or web address based post-search notification.
- Windows 7 - Windows 11 (including XTS-AES and Disk Space Only encryption modes).
BitLocker Password allows you to scan local drives and attached USB devices for BitLocker encryption records. Administrative privileges are required (direct disk access) in order to read BitLocker encryption records. Encryption records loaded can be exported to a file to be processed later or using a different PC. BitLocker Password can also be used to scan partition and drive image files for BitLocker volumes. Number of Backup / Imaging / Cloning tools or bootable Live USB / CD / SD toolkits can be used to create byte-for-byte partition or disk copy (image, clone) if direct mount is not an option (unremovable, voids warranty, etc.).
BitLocker encrypted volumes are protected with 256-bit long random Master keys. Master keys are saved several times encrypted with different access keys (e.g. Recovery key, TPM key, Password to unlock based key, etc.). Most Access keys are 128+bit long random numbers and there is no way to brute-force them directly in any realistic timeframe, thus user supplied password to unlock is the weakest point. Password to unlock is required by default for BitLocker to Go removable volumes and optional for internal disks.BitLocker Password allows you to search for volume password to unlock if it was set. Password verification is extremely compute-intensive (about 2 millions of SHA256 calculations per password), thus recovery speed is limited and a good CPU / GPU hardware is required to achieve fast recovery speed. With BitLocker Password you can queue several attacks including advanced mixed attacks (combinations of dictionary, brute-force and fixed parts) to exploit known password details (parts and patterns) and limit search range and time.
The final password recovery speed is equal to CPUspeed + GPU(1)speed + ... + GPU(N)speed.
For example: Intel i3 + integrated HD 4400 GPU + AMD R9 270 = 16 + 7 + 275 = ~300 p/s (passwords per second).
| CPU: |
|---|
| Instructions: |
| Speed: |
| Intel® Core™2 Duo T7500 @ 2.20GHz |
Intel® Core™ i3 2100 @ 3.10GHz |
Intel® Core™ i3 4130 @ 3.40GHz |
Amazon EC2 "c5.large" Xeon® Platinum core |
|---|---|---|---|
| SSE2 | AVX | AVX2 | AVX512 |
| ~4 p/s | ~8 p/s | ~16 p/s | ~25 p/s |
Integrated GPUs
Modern integrated GPUs (like Intel HD and Iris Graphics) can be used for password recovery acceleration. Integrated GPUs are not as powerful as dedicated (discrete) devices and often overlooked but can add up to 30% to CPU performance.
AMD and Nvidia GPUs
Compute units or stream multiprocessors (CU, SM, SMX, SMM) are the main building blocks of GPU calculation power, thus 32xCU GPU card is usually twice as fast as 16xCU GPU card of the same family and architecture running at the same frequency.
You can expect approximately 20-30 p/s performance per every Nvidia SM running at 1000Mhz and approximately 15 p/s per every AMD CU.
| Tesla K80 (Kepler 2.0) 2x13xSMX, 820 MHz |
GTX 1080 Ti (Pascal) 28xSM, 1580 Mhz |
Tesla V100 (Volta) 80xSM, 1380 Mhz |
RTX 2080 Ti (Turing) 68xSM, 1540 Mhz |
|---|---|---|---|
| + 500 p/s | + 1 400 p/s | + 2 700 p/s | + 2 800 p/s |
| 500/26/0.82=23 | 1400/28/1.58=31 | 2700/80/1.38=24 | 2800/68/1.54=27 |
| HD 6770 (VLIW5) 10xCU, 850 Mhz |
R9 270 (GCN 1.0) 20xCU, 950 MHz |
RX 480 (GCN 4.0) 36xCU, 1260 MHz |
RX Vega 64 (GCN 5.0) 64xCU, 1500 MHz |
|---|---|---|---|
| + 140 p/s | + 270 p/s | + 700 p/s | + 1 400 p/s |
| 140/10/0.85=16 | 270/20/0.95=14 | 700/36/1.26=15 | 1400/64/1.50=15 |
It is important to mention that AMD and NVIDIA architectures are quite different and although AMD per CU performance is lower, there are more CUs per card in a similar price range. Moreover GPU performance is somewhat variable with number of factors including GPU/CPU combination and even a driver version. Please contact us if your recovery speed is noticeable different from the data above.
Trial version can be used to check format and hardware compatibility. It allows you to setup and test run any password search for up to 15 min per run. Recovered passwords are hidden behind the asterisks.
All trademarks are the property of their respective holders.