QuickBooks Forensics
QuickBooks Forensics by Thegrideon Software is a unique tool for QuickBooks company files access, analysis, review, export and recovery as well as password replacement and recovery. It is designed to provide full access to all data saved in QuickBooks database. It works with files directly without any external libraries or database engines! QuickBooks Forensics is also a Transaction Log ('.TLG' files) examination tool. All versions and editions from QB 2006 up to the latest QuickBooks 2024 are supported (Pro, Premier, Accountant, Enterprise, US, CA, UK, ...). Support for versions prior to 2006 and QuickBooks for Mac is limited: password replacement and recovery only.
QuickBooks Forensics Features:
- Direct read-only access to QuickBooks company files:

- lists all database tables with schemas (columns names, types, sizes, etc.);
- protected records are decrypted automatically.

- table viewer is available for preliminary analysis;
- search for records in all or selected tables;
- tables can be exported as XML or CSV files (bulk export is available)
- previews attached binary or large text blocks in a Hex viewer;
- preferences, system settings, update history and last active users are pre-loaded for review;
- All data pages are scanned for recoverable (deleted, lost) tables and records.
- QuickBooks Transaction Logs ('.tlg' files) viewer.

- '.qbw' / '.tlg' files can be extracted from '.qbb' backups.
- SQL Anywhere database UID & PWD Calculator.
- Admin-level user password can be replaced instantly regardless of length or complexity.

- Several attacks can be configured and queued for any user password recovery:

- common brute-force and dictionary attacks with modifications and filtering options;
- advanced mixed attacks for precise search range setup;
- multi-position moves to cover modern password policies;
- simple modifications: add part(s) copy, replace chars, etc.
- typing errors, case switching, char substitutions;
- highly optimized code (SSE, AVX, AVX2, AVX512) guarantees peak performance;
- AMD and NVIDIA GPUs can be used in Quickbooks 2018-2024 password recovery;

- External Apps records are loaded from '.qbw', '.lgb' and '.sdu' files.
- SQL scripts can be extracted from '.qbx' and '.qbm' archives.
- QB Point of Sale backup extraction and data preview.
- Several common tasks can be automated.
- All common versions and editions are supported including QB 2024.
- Windows 7 - Windows 11.
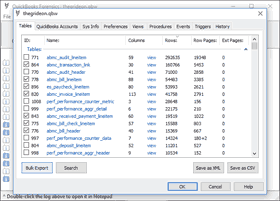
Program Screenshots:
Data Access, Analysis, Review, Export and Recovery
QuickBooks company files are based on SQL Anywhere database engine and any digital analysis is challenging due to the nature of database engine workflow: there are automatic cleanups and optimizations (data pages are being moved, cleared or deleted); file is modified even prior to user login with database startup details and counters; there are lots of SQL functions, events and triggers involved.
QuickBooks Forensics is designed to provide full direct read-only access to all tables (records) saved in QuickBooks '.qbw' files. It is based on reverse-engineering of database format and works with files directly without any database engines. Additional technical details are available for data analysis (for example precise timestamps are present in most tables). Data is not changed in any way and can be accessed or extracted repeatedly in contrast to standard access methods. It is the first tool to offer low-level data access to QuickBooks company files. QB Forensics also searches and recovers old records / discarded data pages with old or lost data.
QB database tables can be previewed for preliminary analysis and / or exported as XML file with proper XSD schema to be used in MS Access, Excel, etc. Search feature is available to look for specific records in all or selected tables.
User preferences, system settings, access history, Apps details and other parameters are pre-extracted and shows to simplify data review and analysis. Attached binary and text blocks of data can be previewed in internal Hex viewer or extracted for further analysis.
UID & PWD Calculator is available to assist in company files data editing in SQL Anywhere.
QuickBooks Forensics can also be used to extract QB Point of Sale backups ('.qpb' files) and preview POS 'qbpos.db' databases. Please contact us for QBPOS password recovery and UID / PWD generation.
Transaction Logs
'.TLG' files are database transaction logs (history of all actions executed by the database engine). The transaction log is a key component of backup and recovery. QuickBooks Forensics sorts log transactions based on tables affected, thus tables history can be tracked step by step.
You can also check our notes on how to learn QB internals from QuickBooks Transaction Logs.
Sensitive Data:
Small subset of data is called "sensitive data" and includes: CC numbers, SSNs, Tax IDs, SINs, company EIN and Bank accounts and routing numbers. It is encrypted with "sensitive data keys".QuickBooks Forensics can decrypt them automatically without any additional data using number of security flaws (QB 2016 upto R5 [up to May 2016] or with '.SDU' files in QB 2017 upto R4 [up to Jan 2017], ...).For patched versions there are number of ways to recover sensitive keys: enter known password or use password recovery for any company file user, export sensitive data keys from an old version (with recoverable keys, known passwords, ...) and import into current versions.
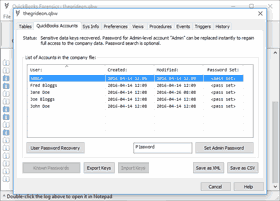
Password Replacement:
Please check our notes on QuickBooks Password Replacement.
Password verification values can be replaced instantly in order to regain access to protected company files. Sensitive data encryption keys are usually recoverable, thus full data access can be restored. Even in worst case scenario (unrecoverable keys, all users with very complex passwords, no prior versions to export keys from, etc.) you still can replace QuickBooks "Admin" password and open company data file, but without access to credit card, tax and bank account numbers, if any are present.
Password Recovery:
User password might be useful outside of the QB environment, therefore password search is available for Admin and non-Admin accounts. QuickBooks Forensics allows you to queue several attacks for precise search range setup including a very flexible mixed attacks (combination of wordlist, brute-force and fixed parts). Additional modifications are available: keyboard layouts-aware recovery technique, char replacement (e.g. I or i with 1), etc.We did our best to enhance this tool performance as well as the recovery speed with some advanced methods and it found to be the fastest tool for QuickBooks password recovery.
Password recovery speed:
Password recovery speed is variable depending on additional information recoverable from the file, username, etc.
The following table is based on several tests with the common laptop, workstation and tablet CPUs (Mp/s = million passwords per second):
| CPU: |
|---|
| Instructions: |
| Up to QB 2017: |
| QB 2018 - 2024: |
| Intel® Atom™ Z3740 @ 1.33GHz |
Intel® Core™ i3 2100 @ 3.10GHz |
Intel® Core™ i3 4130 @ 3.40GHz |
Amazon EC2 "c5.large" Xeon® Platinum core |
|---|---|---|---|
| SSE2 | AVX | AVX2 | AVX-512 |
| 2 - 13 Mp/s | 5 - 25 Mp/s | 10 - 35 Mp/s | 14 - 45 Mp/s |
| 5 700 p/s | 9 000 p/s | 19 000 p/s | 27 000 p/s |
QuickBooks 2018-2024 password recovery with AMD and NVIDIA GPUs:
GPU support was added in QuickBooks Forensics to enhance performance of QB 2018-2024 password search. Several GPUs can be used in parallel to accelerate recovery even more. Below you can see several examples with entry-level, mid-level and enterprise-level cards.
| GT 640 | GTX 470 | HD 6770 | R9 270 | Tesla V100 |
|---|---|---|---|---|
| + 50 000 p/s | + 90 000 p/s | + 120 000 p/s | + 300 000 p/s | > 2 000 000 p/s |
Trial version is available to check format compatibility. It allows you to preview odd rows from any table. Export is enabled for tables "SYS..." and "ISYS...". Protection details are shown, but password replacement is disabled. You can setup and test run any password search for 15 min per set.
All trademarks are the property of their respective holders.